Multi Factor Authentication (MFA) reduces the risk of compromise by 99.9%. Therefore, it is a good idea to use it for every user in an organization. This article provides step-by-step instructions for setting up MFA with the Microsoft Authenticator app on a smartphone. If you have MFA enabled and you switch to a new device, follow the steps here.
My colleague Martina Grom (@magrom) points out the importance of using MFA at every security session, as here at Modern Workplace Conference Paris 2019 last December. Thanks for your support to write this article, Martina.
We often get requests from users how they can change their MFA setup. So here´s the detailed guide how to switch MFA of an existing account to a new device. In this sample, an outlook.com account is guest in an organization where MFA is enabled for every account. Remember, you need to have the "old" device with the Authenticator app available to follow the steps and to register the "new" device with the Authenticator app. Here, I used my old iPhone and my new phone.
Another stumbling block often is, when one account is guest in multiple Azure ADs. Some tenants require MFA and others don´t. So, how can you change the MFA settings to a new device for a specific Azure AD tenant? In this sample, I wanted to change the MFA settings to a new device for a specific tenant. This can be tricky, so here´s the guide for accomplishing that task.
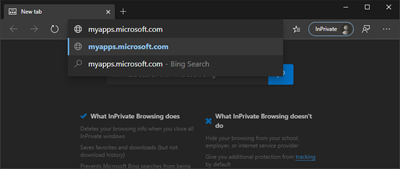
- Open a browser in the "InPrivate mode" and navigate to https://myapps.microsoft.com. You can use the address http://aka.ms/mfasetup alternatively.
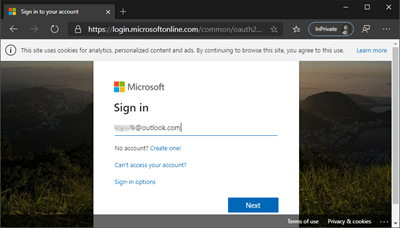
- Sign in with your user name and password.
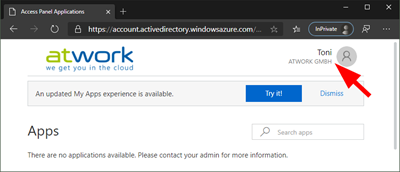
- After a successful login, you get redirected to https://account.activedirectory.windowsazure.com/r#/applications. See the connected tenants in the user menu on the top right corner as here. Every tenant where the user is added as guest, shows up here.
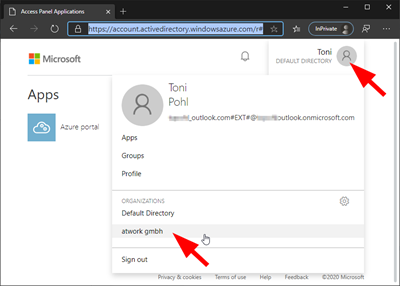
In this sample, there are only two directories available; The "Default Directory", and another Microsoft 365 tenant "atwork…". - Now switch to the "other" Azure AD, where the user is guest, here to "atwork…" as shown in the screenshot above.
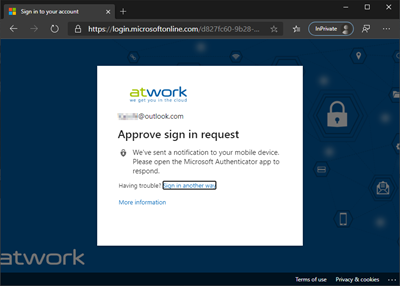
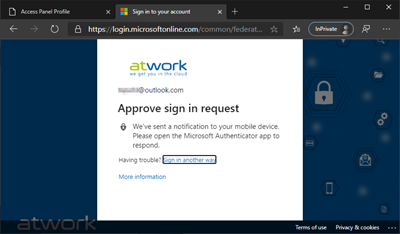
- Sign in to the other Azure AD. Confirm with your "old" Authenticator app or with the second factor.
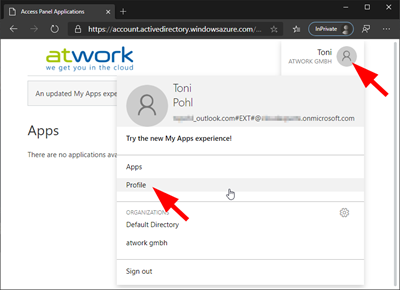
- The tenant has been switched to the new Azure AD "atwork…" as we see here.
- Again, open the user menu. In here, open "Profile" as we see here.
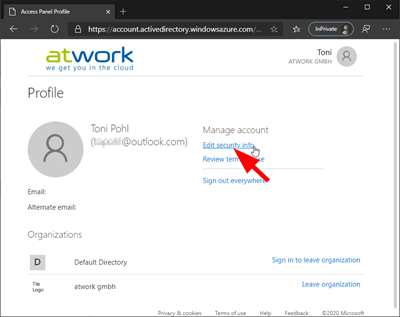
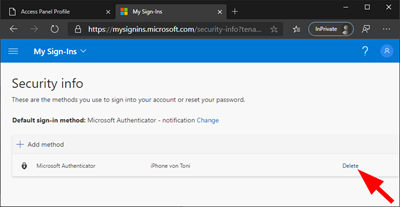
- In the profile page, select "Edit security info".
- Another browser tab with the Sign in dialog opens. Select "Remain signed in with this account".
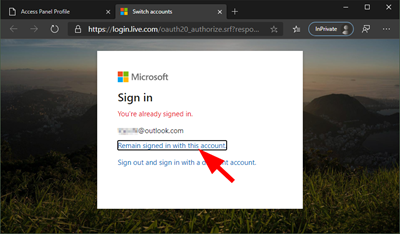
- Now sign in again with your "old" Authenticator app or the second factor.
- Ok, we now can edit the Authenticator app. We recommend to remove the old Authenticator app first. In my sample, I click "Delete" the Microsoft Authenticator at "iPhone of…". Confirm the deletion.
- Now, we add the account to the Authenticator app on the new device.
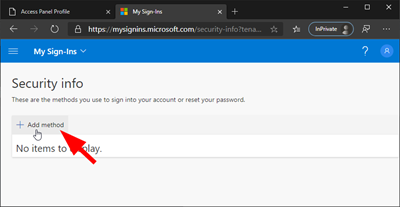
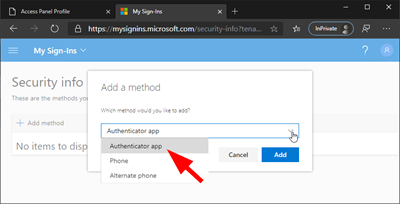
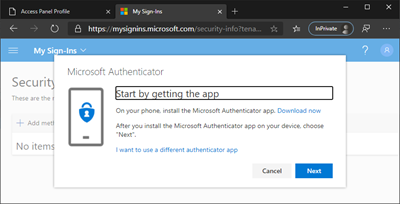
- Add the preferred second factor authentication method "Authenticator app" and click "Add".
- Click "Next". (We assume, you have installed the Authenticator app already on your new device).
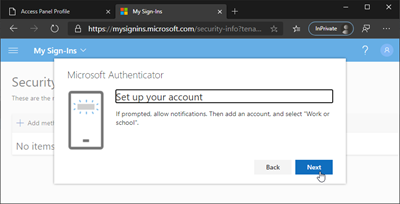
- Confirm and click "Next".
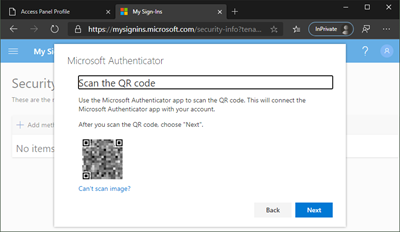
- Use your phone and scan the code in the Authenticator app.
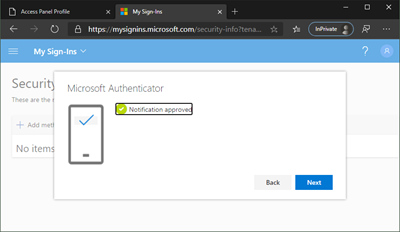
- When the code is scanned, try it out. Microsoft sends a sign-in command asking for the second factor, now on your new device. "Approve" the sign-in request on your phone
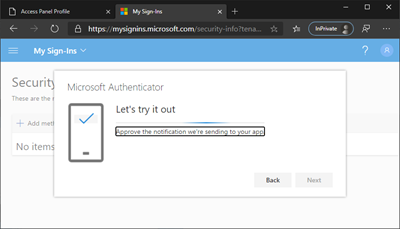
- When successfully done, click "Next".
- Done. Your new device will show up.
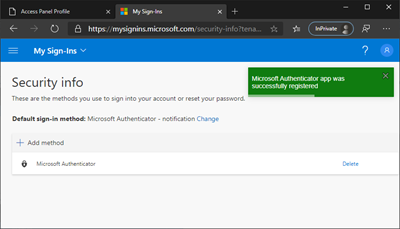
- You can now sign-out or close the browser.
- Then, remove the account from the old device (or wipe it when ready…).

(Royalty-Free photo from www.dreamstime.com.)
See the Set up the Microsoft Authenticator app as your verification method article as well.
We hope, this article helps for securing your accounts with Multi Factor Authentication and to make it easy to change devices for accounts with MFA.
Categories: App, Azure, Cloud, English, Microsoft, Microsoft365, Office365, Security
Source: https://blog.atwork.at/post/setup-the-MFA-Authenticator-app
