Governance specifies the rules for an organization. The Office 365 collaboration platform allows to invite external users for contributing in groups. In this part, we want to monitor all groups that have external guests and inform the group owners, who has access to a group or a team. See how this works here.
Get all groups with external guests
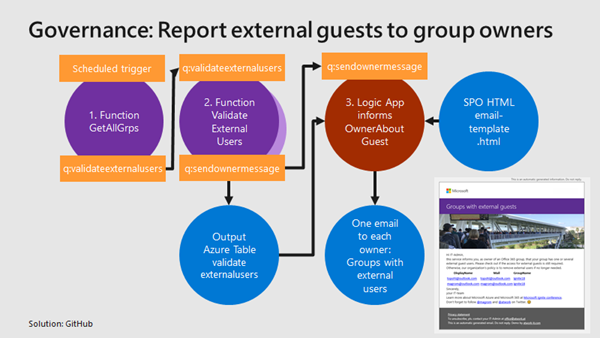
We use the same mechanism as before, see the article about Orphaned Groups. A function runs e.g. every day, reads all existing groups in the Office 365 tenant, and writes each group in a queue. A second function is triggered by that queue and reads all the external group members for one group. The following graphics shows that process from a technical standpoint.
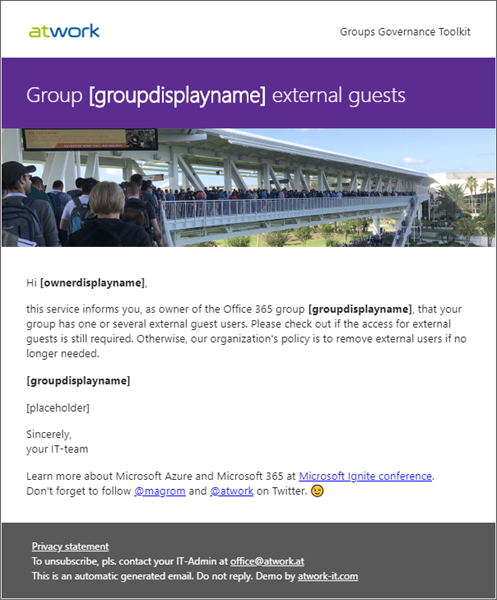
Again, we are using an Azure storage account for providing the queue for the communication between the two functions, and a table for storing the result of the functions. For each group with external members, we use a Logic App that generates an email to the group owner, informing him or her about the external users. The email template is stored in SharePoint Online. That's easy to access from a Logic App and the template can be modified easily. The template could look similar as here, using [placeholder] text for the data we want to insert.
So, the HTML file is stored in a SPO document library (or in Azure Blob storage, or somewhere else…).
Create the Azure Functions…
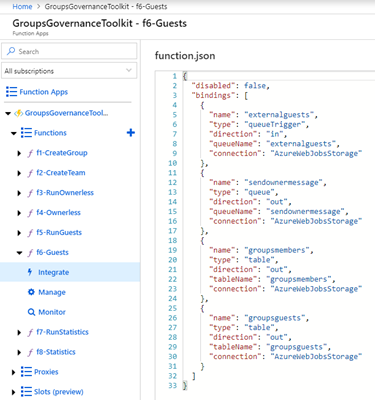
Create two new Azure Functions as in the article before, and paste the code for f5-RunGuests and f6-Guests into your code window. For communicating, we are using the bindings. Adapt them as provided at f5-RunGuests/function.json and f6-Guests/function.json. The screenshot below shows the new bindings for f6-Guests/function.json: The queue is accessed by the name "externalguests", the result will be written to table "groupsguests". Additionally, every group owner gets an email. This is controlled by writing to queue "sendownermessage". A Logic App listens to that queue and sends the email.
Finally, the Logic Apps
To use the External Groups functions daily, Azure Logic App help. We use two Logic Apps:
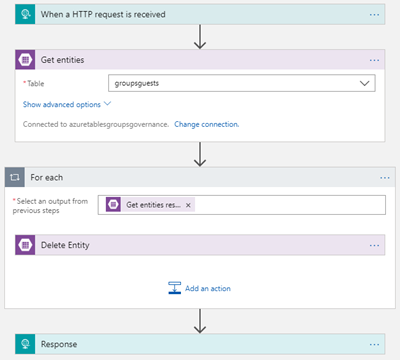
The first simply one, "ClearGroupsGuests", deletes all data that might be existing in out target table "groupsguests". We could delete the whole table and regenerate it, or run through all records and delete them. Anyway, as result, the table shall be empty, so we can insert new data. This Logic app is called from our function code f5-RunGuests at the beginning and looks as here.
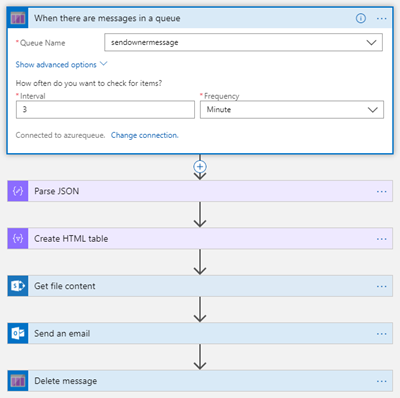
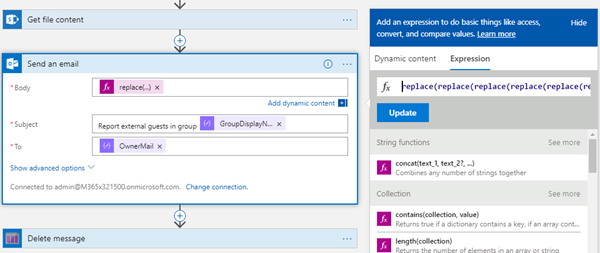
The second LogicApp "GroupsGuests" listens to queue "sendownermessage", reads all records from the Azure table "groupsguests", creates a HTML table out of it, loads the email template from a SharePoint Online document library and finally creates an email to the group owners. The body placeholders are replaced by data from the table "groupsguests".
The send an email part contains multiple replace functions.
As expression in the email Body property, this functions are used:
replace(replace(replace(string(body('Get_file_content')),'[placeholder]',string(body('Create_HTML_table'))), '[groupdisplayname]',body('Parse_JSON')?['GroupDisplayName']), '[ownerdisplayname]',body('Parse_JSON')?['OwnerDisplayName'])
Let it run
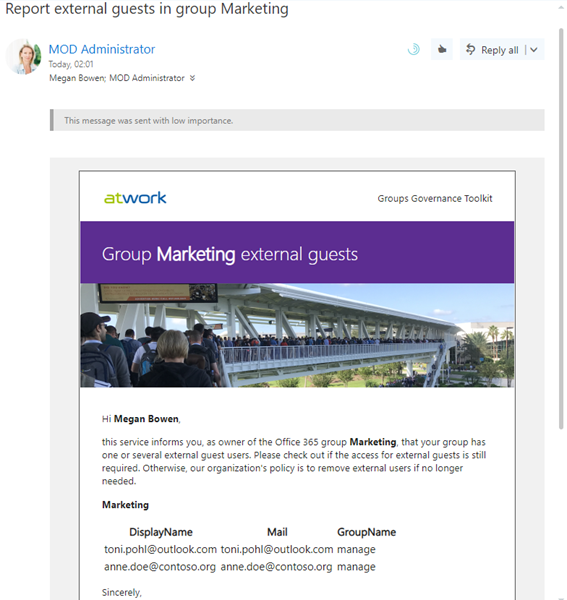
When f5-RunGuests is executed, it will run through all groups in the Office 365 tenant, and call f6-Guests for each group which fills the Azure table "groupsguests" and writes into the queue "sendownermessage". The Logic App generates an email with that output. This could look similar as here.
Each group owner gets informed about external guests in his or her groups and can check if the user's access is still necessary or not. This process helps to make existing Office 365 Groups and Teams compliant once and in daily life.
See the full groups statistics in the next article.
Office 365 Groups Governance Toolkit series
See all parts of the Office 365 Groups Governance Toolkit series here:
- Part 1 - Overview
- Part 2 - Provisioning requirements
- Part 3 - Develop Azure Functions
- Part 4 - Ownerless Groups
- Part 5 - External Guests
- Part 6 - Groups statistics
- Part 7 - Working with Group Policies
Categories: atwork, Azure, Cloud, Developer, English, Microsoft, Microsoft365, MVP, Office, Office365, PowerShell, SharePoint
Source: https://blog.atwork.at/post/Groups-Governance-Toolkit-Part-5-External-Guests